For deployment in on-premises environments, we recommend a standard deployment topology consisting of one or more AD FS servers on the internal corporate network, with one or more Web Application Proxy (WAP) servers in a DMZ or extranet network.
Where should ADFS be installed?
As a security best practice, place Active Directory Federation Services (AD FS)federation servers behind a firewall and connect them to your corporate network to prevent exposure from the Internet. This is important because federation servers have full authorization to grant security tokens.
Should servers in the DMZ be on the domain?
Therefore, given the immense importance of keeping it protected, placing a domain controller in DMZ is not a preferable solution. The most common solution we experience is placing DMZ servers as standalone. … With windows 2008 R2 directory there is a possibility of extending domain in DMZ by placing RODC.
What ports need to be open for ADFS?
ADFS incoming is port 443/https and the ADFS server needs pretty much any port open to AD. The DirSync server needs also all ports open to AD and 443/https to Office 365 plus port 80 to verify the Certificate Revocation List of the O365 server. Your TMG server has 443/https incoming and outgoing to the ADFS server.Does ADFS need to be installed on domain controller?
“Because ADFS requires the installation of Internet Information Services (IIS), we strongly recommend that you not install any ADFS components on a domain controller in a production environment.”
Is Azure AD the same as ADFS?
Azure AD vs AD FS Although both solutions are similar, they each have their own distinctions. Azure AD has wider control over user identities outside of applications than AD FS, which makes it a more widely used and useful solution for IT organizations.
What is the purpose of ADFS?
ADFS allows users from one organization to access applications of partner organizations using the standard credentials of their organization’s Active Directory (AD). ADFS also lets users access AD-integrated applications while working remotely using their standard organizational AD credentials via a web interface.
How do I expose ADFS Internet?
The ADFS server should not be exposed on the open internet. If users need to be able to use ADFS sign-in from outside the internal network of the organization, then the solution is to set up a web application proxy on a separate server in the DMZ.What protocol is used for ADFS?
The protocol used between WIF and ADFS is WS-Federation. If the STS was Java based (e.g Ping Identity or OpenAM), then WIF would use the SAML protocol for communication. ADFS also supports SAML to enable federation.
What is ADFS and ADFS proxy?The purpose of the ADFS proxy server is to receive and forward requests to ADFS servers that are not accessible from the internet. ADFS proxy is a reverse proxy and typically resides in your organization’s perimeter network (DMZ). The ADFS proxy plays a critical role in remote user connectivity and application access.
Article first time published onAre domain controllers in the DMZ?
However, Internet applications nowadays sometimes demand access to your network. You can help increase security by putting domain controllers in a DMZ. … Servers that typically go into the DMZ are servers that need to be exposed to the Internet, such as Web servers and e-mail servers.
What is DMZ domain?
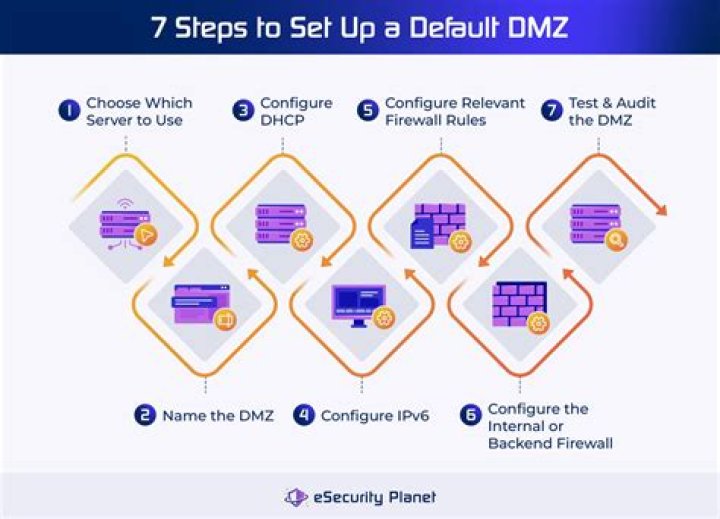
In computer security, a DMZ or demilitarized zone (sometimes referred to as a perimeter network or screened subnet) is a physical or logical subnetwork that contains and exposes an organization’s external-facing services to an untrusted, usually larger, network such as the Internet.
What is Rodc server?
A read-only domain controller (RODC) is a server that hosts an Active Directory database’s read-only partitions and responds to security authentication requests.
How do I protect AD FS?
Hardening your AD FS servers Ensure only Active Directory Admins and AD FS Admins have admin rights to the AD FS system. Reduce local Administrators group membership on all AD FS servers. Require all cloud admins use Multi-Factor Authentication (MFA). Minimal administration capability via agents.
What are AD FS endpoints?
Endpoints provide access to the federation server functionality of AD FS, such as publishing federation metadata. To verify that the AD FS server is responding to web requests, we can check the various endpoints.
Does AD FS require Active Directory?
All AD FS servers must be a joined to an AD DS domain. All AD FS servers within a farm must be deployed in a single domain.
What are the components of ADFS?
- Active Directory: This is where all the identity information is stored to be used by ADFS.
- Federation server: Contains the tools needed to manage federated trusts between business partners, and hosts the “Federation Service” role service of ADFS.
What are ADFS claims?
A claim is a statement about a user that is used for authorization purposes in an application. ADFS brokers trust between disparate entities by allowing the trusted exchange of arbitrary claims that contain arbitrary values. The receiving party uses these claims to make authorization decisions.
How do I use ADFS?
- Step 1: Install Active Directory Federation Services. …
- Step 2: Request a certificate from a third-party CA for the Federation server name. …
- Step 3: Configure ADFS. …
- Step 4: Download Office 365 tools. …
- Step 5: Add your domain to Office 365. …
- Step 6: Connect ADFS to Office 365.
Do you need ADFS in Azure?
Federation with Azure AD or O365 enables users to authenticate using on-premises credentials and access all resources in cloud. As a result, it becomes important to have a highly available AD FS infrastructure to ensure access to resources both on-premises and in the cloud.
Why is Azure AD better than ADFS?
Using Azure AD as a primary authentication method will lower the risk of a breach versus relying on ADFS. Azure AD is more equipped to provide security safeguards due to several features such as multi-factor authentication and conditional access to ensure that the right users have the right access.
What replaces ADFS?
Can I replace ADFS with AD Connect Seamless Sign-On? The simple answer is ‘yes’! Microsoft released an update to Azure AD Connect in June 2017 called Seamless Single Sign-On (also known as SSO) that offers a simpler and more cost-effective SSO solution for Office 365 than ADFS.
How do you test if ADFS Proxy is working?
To verify that a federation server proxy is operational On the Start screen, typeEvent Viewer, and then press ENTER. In the details pane, double-click Applications and Services Logs, double-click AD FS Eventing, and then click Admin.
Does Adfs use IIS?
On Windows Server 2012, IIS is required for AD FS. Version 3.0 that comes with Windows Server 2012 R2 does not require IIS to be installed.
What servers should be in the DMZ?
Any service provided to users on the public internet should be placed in the DMZ network. External-facing servers, resources and services are usually located there. Some of the most common of these services include web, email, domain name system, File Transfer Protocol and proxy servers.
Why do you need a DMZ?
DMZ’s are an essential part of network security for both individual users and large organizations. They provides an extra layer of security to the computer network by restricting remote access to internal servers and information, which can be very damaging if breached.
What are the disadvantages of DMZ?
Disadvantages. Setting up the DMZ is something that not everyone knows how to do, so doing it the wrong way can lead to the possibility of lose or suffer from some kind of copy in all the information that the system has.
What is RODC and Rwdc?
An RODC is a new domain controller (DC) mode in Windows Server 2008. … A read-only AD Domain Services (AD DS) database–Applications that need only database read access can use the RODC; however, any database changes must be made to a read-writable DC (RWDC), then replicated back to the RODC.
How can you tell DC from RODC?
In ‘Active Directory Users And Computers’ browse to the RODC’s computer object the DC Type should contain say ReadOnly if it is a RODC. The computer object properties on tab ‘Managed by’ should also show what type of DC it is.
What is the difference between DC and RODC?
The difference is that a DC holds writable files containing sensitive data, such as passwords, about all users and computers throughout the domain. … An RODC, on the other hand, stores read-only data about a subset of users and computers in the domain which it has been authorized to authenticate.
What is a potential security risk when AD FS?
The vulnerability discovered leads to security issues that create a wide scale denial-of-service against exposed organizations, and potentially, identity compromise. …