Insufficient data protection (communication and storage) The most frequent concerns in the data security of IoT applications are due to insecure communications and data storage. One of the significant challenges for IoT privacy and security is that compromised devices can be used to access confidential data.
What are the main challenges of Internet of Things IoT?
- Lack of encryption – …
- Insufficient testing and updating – …
- Brute forcing and the risk of default passwords – …
- IoT Malware and ransomware – …
- IoT botnet aiming at cryptocurrency –
What is IoT in security?
IoT security is the technology segment focused on safeguarding connected devices and networks in the internet of things (IoT). … Allowing devices to connect to the internet opens them up to a number of serious vulnerabilities if they are not properly protected.
What are the issues and challenges in Internet of things?
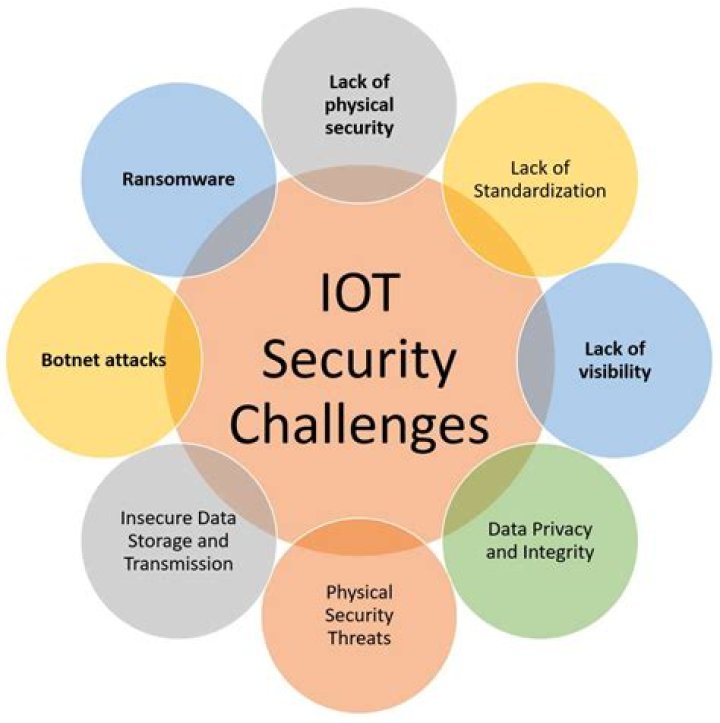
Five key IoT issue areas are examined to explore some of the most pressing challenges and questions related to the technology. These include security; privacy; interoperability and standards; legal, regulatory, and rights; and emerging economies and development.Why security is important in IoT?
Hardware, software and connectivity will all need to be secure for IoT objects to work effectively. Without security for IoT, any connected object, from refrigerators to manufacturing bots, can be hacked. Once hackers gain control, they can usurp the object’s functionality and steal the user’s digital data.
What is the impact of IoT in security and surveillance?
IoT security solutions allow organizations to: Gain greater visibility over who enters and leaves a facility in real-time. Consistently and securely monitor facility conditions from any location with Wi-Fi access. Act quickly on important security alerts delivered right to their mobile device.
Why we need IoT security explain security and privacy issues for IoT?
IoT devices are connected to your desktop or laptop. Lack of security increases the risk of your personal information leaking while the data is collected and transmitted to the IoT device. … So if the IoT device contains any security vulnerabilities, it can be harmful to the consumer’s network.
What are the security challenges?
- #1: Navigating the cybersecurity skills gap. …
- #2: Defending against evolving security threats. …
- #3: Complex environments and operations. …
- #4: Demanding compliance mandates. …
- #5: Maintaining business speed. …
- #6: Cloud native applications. …
- #1: Navigating the cybersecurity skills gap.
What are the security and surveillance challenges in IoT?
Poor IoT device management. IoT malware and ransomware. IoT botnets aiming at cryptocurrency. Data security and privacy concerns.
What is a security issue?A security issue is any unmitigated risk or vulnerability in your system that hackers can use to do damage to systems or data. This includes vulnerabilities in the servers and software connecting your business to customers, as well as your business processes and people.
Article first time published onWhat are the contemporary security challenges?
The topics to be covered are likely to include war and conflict, nuclear weapons, terrorism, cyber threats, the UN, drone violence, disease and security, the environment and climate change, and intelligence and the surveillance state.
What are the security issues in cloud computing?
- Lack of visibility into what data is within cloud applications.
- Theft of data from a cloud application by malicious actor.
- Incomplete control over who can access sensitive data.
- Inability to monitor data in transit to and from cloud applications.
How does culture influence security issues?
Individuals and small groups, basing their worldview on their own cultural consumption and acting on their own conception of reality, can pose security threats. The atomizing effects of technology help to secure their assumptions. And their influences can come from anywhere in the world.
What is the concept of human security?
Human security means protecting fundamental freedoms – freedoms that are the essence of life. It means protecting people from critical (severe) and pervasive (widespread) threats and situations”. Human security integrates three freedoms: freedom from fear, freedom from want and the freedom from indignity. •
What is meant by system vulnerability and abuse?
System Vulnerability and Abuse. When data are stored in digital form, they are more vulnerable than when they exist in manual form. Security refers to the policies, procedures, and technical measures used to prevent unauthorized access, alteration, theft, or physical damage to information systems.
What are the challenges and risks associated with cloud security?
lack of cloud security architecture and strategy. insufficient identity, credential, access and key management. account hijacking. insider threats.
What are the major challenges faced in cloud?
- Security.
- Password Security.
- Cost Management.
- Lack of expertise.
- Internet Connectivity.
- Control or Governance.
- Compliance.
- Multiple Cloud Management.
Why is security important in life?
Human security is concerned with safeguarding and expanding people’s vital freedoms. It requires both protecting people from critical and pervasive threats and empowering people to take charge of their own lives. … States have the fundamental responsibility of providing security.
What are the three types of security?
There are three primary areas or classifications of security controls. These include management security, operational security, and physical security controls.
Why do we need it security?
Reducing the risk of data breaches and attacks in IT systems. Applying security controls to prevent unauthorized access to sensitive information. Preventing disruption of services, e.g., denial-of-service attacks. … Providing peace of mind by keeping confidential information safe from security threats.